全てのランナーの
やった!できた!
がこのサイトに!
お知らせ
News
-
 お知らせ
お知らせ
大阪ハーフマラソン2023!結果報告
2023/1/29 大阪ハーフマラソン2023に出場してきました! youtube 結果は1:15’24”でPB更新でした! ※ネットタイム 前回1:18’56”(2020年大阪ハーフマラソン) から3分32秒タイムを更 […] -
 お知らせ
お知らせ
東京でのパーソナルレッスンを開始します
当サイトの運営は大阪に店舗を構えるの大人のRUNトレ塾が行っております! 大人のRUNトレ塾にて実際にランナーの皆様にパーソナルレッスンを行っているのですが、 そのレッスンを東京でもさせて頂けることになりました! 詳細は […] -
 お知らせ
お知らせ
2022年おかやまマラソンPB更新
おかやまマラソン2022を走ってきました! 雨の中のレースでしたが、気温はちょうどよく無事完走できました! 今回は私の結果報告! 結果 結果2:38’25” PB前半1:18’35”後半1:19’50” 前回の2:42’ […]
アバウト
About
初めまして!
大人のRUNトレ塾の代表吉野と申します!
大阪南森町に店舗を構え、市民ランナーに特化したランニングフォーム改善のトレーニング指導を行っております!
各種SNSやメディアで取り上げられ、自身でもYoutubeにて発信!
こちらのHPでは市民ランナーの皆さんのお悩みを解決するブログをまとめております!
実店舗で指導しているトレーニング内容や理論などを動画販売しておりますので、ぜひご覧ください!
大人のRUNトレ塾の代表吉野と申します!
大阪南森町に店舗を構え、市民ランナーに特化したランニングフォーム改善のトレーニング指導を行っております!
各種SNSやメディアで取り上げられ、自身でもYoutubeにて発信!
こちらのHPでは市民ランナーの皆さんのお悩みを解決するブログをまとめております!
実店舗で指導しているトレーニング内容や理論などを動画販売しておりますので、ぜひご覧ください!

Contents
このHPサイトで提供しているものを紹介します!ランニングフォームの悩み、練習の質についての悩み、
ランニングによる体の痛み、当サイトで解決します!
動画販売
Video Sales
文章には文章の魅力があり、動画には動画の魅力があります。理論への理解を深めていくためにはブログの文章を、実践的なフォームへの落とし込み・習得には動画をご活用ください。
店舗で実際に指導している実績を活かして常に精度の高い情報をアップロードして販売しております!
店舗で実際に指導している実績を活かして常に精度の高い情報をアップロードして販売しております!

月間100kmメソッド
100km/month Method
解剖学や生理学などの「体の仕組み」と運動学などの「体の動かし方」をもとに理論を作り上げました。その理論を活用して私自身が月間走行距離100kmでフルマラソン2:50切りを実現!無闇に距離を走るだけではなく、体の機能を活用して最大限のパフォーマンスを引き出しましょう!月間100kmでも結果を出せたメソッドをあなたの走りにご活用ください!

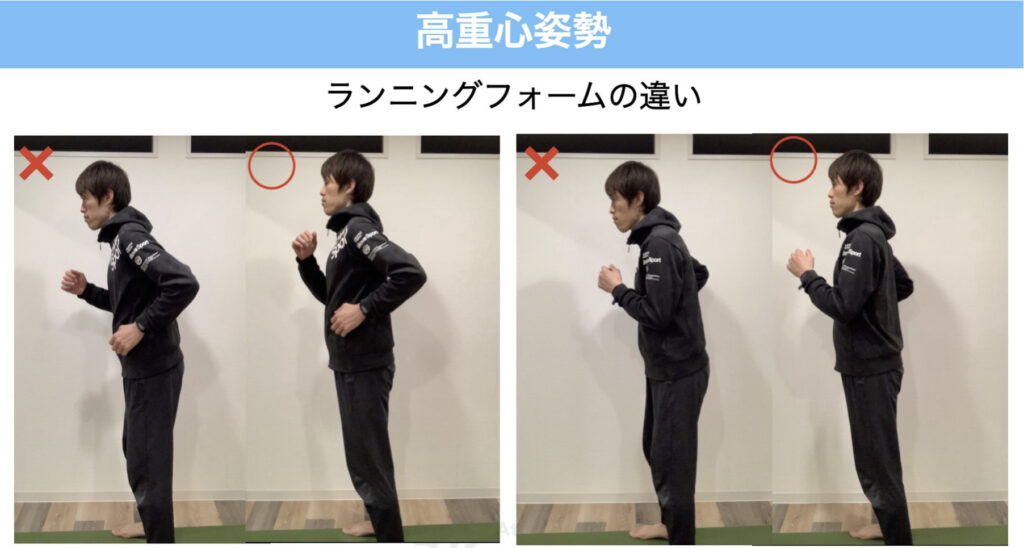
ランニングフォーム
Running Form
練習量をこなしてもタイムが伸びない。多くのランナーの悩みの種です。それは 体力に問題があるのではなく 、ロスの多いランニングフォーム のせいかもしれません。ランニングは手軽に始めやすいために自己流のフォームになってしまいがち。 最初はそれでも良いですが、高みを目指すなら確実に頭打ちが来てしまいます。どんどん進む、楽で周りを魅了する格好いいフォームを身につけましょう!
ランニング力チェックでは、当HP内に記載している内容から独自の問題を作成し、点数化しております!間違えた問題などはブログ内で答え合わせができるようになっているのでぜひ試してみてください!
ランニング力チェックでは、当HP内に記載している内容から独自の問題を作成し、点数化しております!間違えた問題などはブログ内で答え合わせができるようになっているのでぜひ試してみてください!

ランニングの痛み
Running Pain
ランニング中の痛みは本当に辛いもの。故障・痛みを治すために練習を休めば体力は落ちるし、ただ、痛みを放置して練習を続けると、どんどん体はボロボロになり、走れない体になってしまいます。「怪我が癖になってしまっている」「ランニングをしていれば必ずどこかに痛みは出るもの」そうお考えの方は、痛みの原因を改善することで更なる伸び代があります!痛みは誤った体の使い方であることを知らせる合図。 正しい知識があれば、怪我はレベルアップの大きなチャンスなのです!その方法をお伝えします。

Blog
ブログ